Enigma
█ LARRY GILMAN
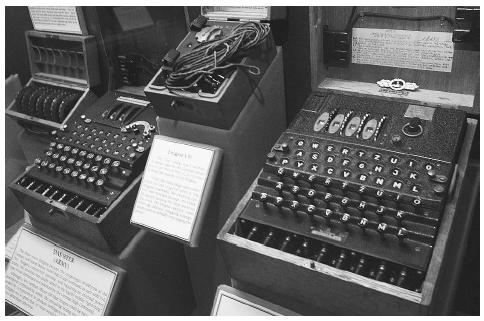
Enigma was a ciphering (code communication) system used by the German military from 1926 until the end of World War II, and by several other nations for some years after. Enigma was the first mechanized message-encryption system to see wide use. Enigma produced such thoroughly scrambled messages that for many years its cipher was considered unbreakable both by the German military and its foes. Polish and British mathematicians, however, cracked the Enigma cipher in time to give the Allies access to most German military communications throughout World War II. The German government never knew that the Enigma cipher had been broken and that its military communications were often transparent, giving a significant advantage to the Allies on many occasions. The Japanese military also used a cipher related to Enigma during World War II. The Japanese version of Enigma was cracked by American cryptographers, providing a crucial advantage to the Allies in the Pacific theater. U.S. knowledge of secrete Japanese transmissions was essential, for example, to victory at the crucial battle at Midway, the Japanese navy's first major defeat in several centuries. Many military strategists and historians hold that Allied success in cracking the Enigma and related ciphers helped significantly shorten World War II.
Origin of Enigma. During World War I, cumbersome paper-and-pencil ciphers were still the rule, as they had been for centuries past. (A cipher is any scheme for transforming ordinary written language— plaintext —into a coded, but apparently random string of characters, ciphertext .) After World War I, several inventors turned their attention to the mechanization of ciphering, seeking to increase accuracy, speed, and security. The most successful of these inventors was German engineer Arthur Scherbius, who in 1918, created a cipher machine he named the Enigma. (This is not a translation; the word "enigma" is the same in German and English). Scherbius was unsuccessful in selling Enigma to commercial buyers. It was not until 1923 that Enigma was chosen by the German government as its standard ciphering system, as Germany had only just learned how much damage had been done by the breaking of its ciphers by the Allies in World War I. Between 1925 and 1945, the German military bought over 30,000 Enigma machines, deploying slightly different systems to its European armies, its army in North Africa, its air force, and its navy.
The Enigma cipher. The Enigma cipher is built upon the simplest of all cipher types, the substitution cipher. In a substitution cipher, one letter of the alphabet is substituted directly for another. A substitution cipher for a sixletter alphabet might appear as:
Plaintext: A B C D E F
Ciphertext: F C A B D E
Using this cipher, the plaintext word BAD (for example) would produce the ciphertext word CFB. Such ciphers are easy to implement, but also contain easily broken code, as their ciphertext contains all the regularities of
ordinary language: that is, double letters in plaintext appear as double letters in ciphertext, the ciphertext letter for "e" will appear in the ciphertext just as often as "e" appears in plaintext, and so forth. Such codes are weak because analyzing regularities is one of the primary means by which codebreakers attack codes.
However, by adding complications to this simple idea, a powerful code can be devised. Consider the following substitution cipher for a three-letter alphabet:
Plaintext: A B C
Ciphertext: A C B
In this simple example, A is enciphered as itself. This cipher can be imagined as a physical device consisting of three disks or dials arranged in a row. The first (left-hand) and third (right-hand) disks, each of which has the alphabet ABC spaced evenly around its edge, are identical, and are aligned so that their letters are in the same positions; the third disk, which sandwiched between the other two, is different. It contains three wires that pass from its left side right through to its right, connecting the two alphabet disks so that the A of the left-hand disk is wired to the A of the right-hand disk, the B of the left-hand disk to the C of the right-hand disk, and the C of the left-hand disk to the B of the right-hand disk. In effect, the middle disk scrambles the alphabet. The result is a simple substitution cipher. If the middle disk, (the scrambler) is rotated, however, so that the wire which touched A on the plaintext disk now touches C on that disk, all the other letters on the plaintext and ciphertext disks will also be connected differently by the scrambler, producing the following substitution cipher:
Plaintext: A B C
Ciphertext: B A C
This can be verified by describing the wires in the scrambler as a set of input-output rules, one for each wire:
- Connect input position 1 to output position 1.
- Connect input position 2 to output position 3.
- Connect input position 3 to output position 2.
By rule 1, when scrambler input position 1 is lined up with the letter A on the left-hand (plaintext) disk, it is connected to output position 1, which is lined up with the letter A on the right-hand (ciphertext) disk. The other two substitutions are produced by the other two wires: B → C, C → B. When the scrambler is rotated so that its input 1 moves from A to C on the plaintext disk, its output 1 moves from A to C on the ciphertext disk. Now, instead of producing A → A, wire 1 produces C → C. The other two wires now produce the substitutions A → B, B → A. Thus, each time the scrambler is rotated by one letter position, a new different substitution code is produced. This continues until the scrambler returns to its starting position, whereupon the substitution codes produced by the device begin to repeat. In this example, repetition begins with the third shift of the scrambler.
Rotation of the scrambler can be used to make a cipher that is more formidable than a straightforward substitution. Consider a three-letter plaintext message is to be sent: ABA. First, A is enciphered with the scrambler in the first position described above: A → A. Before the second letter is encrypted, the scrambler disk is rotated by one letter-position. The second plaintext letter is then enciphered: B → A. The disk is rotated, and A is enciphered again: A → C. Although in this case one would start repeating substitutions after only three letters, the resulting cipher is significantly more complex, and thus harder to crack, than a static substitution cipher.
Decryption in this system is simple as long as the receiving party possesses an identical machine; the wires in the scrambler disk work equally well in either direction, so decryption is simply encryption run backwards. The receiver must, however, begin decrypting with their scrambler set to the same position as the sender's at the start of transmission, otherwise the substitution codes used by the receiver to decipher the message will be out of step with those used by the sender to encipher it, and decipherment will fail.
The Enigma system was based upon the scramblerdisk principle described above. Enigma used not a 3-letter, but a 26-character alphabet and not one, but four scrambler disks. The first scrambler scrambled plaintext or ciphertext, the second scrambler scrambled the outputs of the first scrambler, the third scrambled the outputs of the second, and the fourth fed back, or "reflected," the outputs of the third so that messages passed through the other three scramblers before the encrypted ciphertext (or decrypted plaintext) was read. Each letter was thus scrambled a total of seven times during its passage through the machine. Three of the scrambler disks could be rotated freely, but the fourth, the "reflector," was stationary.
In order to use an Enigma unit, its operator typed plaintext or ciphertext into a keyboard. For each keystroke typed, Enigma automatically shifted one or more of its scramblers and lit up a letter on a display board. The letter on the display board showed the output text for the typed input letter: ciphertext if plaintext was input, plaintext if ciphertext was input. To produce further scrambling between ciphertext and plaintext, each Enigma also had a built-in commutator or "plugboard" that enabled the operator to crisscross paired letters of the alphabet before their signals fed into the first scrambler disk. The result was that Enigma had over 10 20 different "keys" or distinct settings of scramblers and plugboard. Simply guessing the correct key for a given message was, therefore, essentially impossible. Every day at midnight, all operators of a given Enigma system would switch to a new key; these initial daily keys were printed in a codebook that was distributed to the operators. For added security, the scrambler-disks part of the key was changed for every single message sent; this message-key information was transmitted twice at the beginning of every message. This technique was intended to prevent message loss due to transmission errors, but in fact reduced Enigma's effectiveness by introducing an element of predictability.
The defeat of Enigma. Enigma was long considered impossible to crack. However, in 1931, a disgruntled German exofficer gave drawings for the machine to the French secret service. The French, who considered Enigma too tough to crack even with this information in their possession, gave it to the Polish government. Polish mathematician Marian Rejewski (1905–1980) used it to devise automatic devices (specialized electromechanical calculators) for re-cracking the ever-changing Enigma cipher on a daily basis. Just before the fall of Poland in 1939, Rejewski's findings were transferred to the British government, which continued to improve them.
During World War II, the German military modified the Enigma system at intervals, requiring the British to continue re-cracking the cipher throughout the war. With the help of a motley team of crossword-puzzle experts, bridge devotees, chess champions, mathematicians, and linguists led by British mathematician and computing pioneer Alan Turing (1912–1954), the group succeeded. Tragically, however, Turing was persecuted after the war for his homosexuality. His security clearance was revoked, he was forced to undergo debilitating hormone treatments, and he was banned from the development of the digital computer. Turing committed suicide in 1954, some 20 years before his crucial contribution to the cracking of Enigma, and thus, to the Allied victory, was declassified.
█ FURTHER READING:
BOOKS:
Churchouse, Robert. Codes and Ciphers. Cambridge, England: Cambridge University Press, 2002.
Singh, Simon. The Code Book. New York: Doubleday, 1999.
Comment about this article, ask questions, or add new information about this topic: