Fingerprint Analysis
█ AGNIESZKA LICHANSKA
Fingerprints are the patterns on the inside and the tips of fingers. The ridges of skin, also known as friction ridges, together with the valleys between them form unique patterns on the fingers. Fingerprint analysis is a biometric technique comparing scanned image of prints with a database of fingerprints. Uniqueness of prints, and the fact that they do not change during a person's life, form the basis for fingerprint analysis. The uniqueness of the prints is determined by the minute changes in local environment during fetal development; therefore, the identical twins undistinguishable by DNA analysis can be differentiated with fingerprint analysis. Although the fingerprint pattern remains the same, growth accounts for an enlargement of the patterns. Additionally, accidents or some diseases may alter fingerprint patterns
History of fingerprint use. Notes about the ridges, loops, and spirals of fingerprints were first made in 1686 by Marcello Malpighi. However, it was not until 1880 that fingerprints were recognized as a means of personal identification by Henry Faulds, who also identified a first ever fingerprint. The first book about fingerprints was published in 1888 by Sir Francis Galton, and was titled simply Fingerprints. Galton established the first classification system for fingerprints and was the first to assert that no two prints are the same, or that the odds of two prints being identical were about 1 in 64 billion. Later, the Henry Classification System was developed in 1901 by Sir Edward Henry, and today forms the basis for print recognition in most English speaking countries. This system categorized the ridge patterns into three groups: loops, whorls, and arches.
Fingerprinting was soon introduced in prisons, army and widely used for identification by law enforcement. The Federal Bureau of Investigation collection has millions of fingerprint cards and consists of approximately 70 million fingerprints. Although the main use of prints remains in forensic science and law enforcement, new uses of fingerprints have been developed.
Detection of fingerprints. Presence of pores on the surface of the ridges of the fingers results in the accumulation of perspiration on the fingertips. This moisture remains on the surface of the object a person touches, leaving prints. Depending on the surface touched, prints can be visible to the naked eye (e.g. metal, glass or plastic) or invisible (paper, cardboard or timber). Prints left on non-porous surfaces such as metal can be visualized with powders and lifted with tape. In contrast, the prints on porous objects require special lighting, such as lasers or x rays.
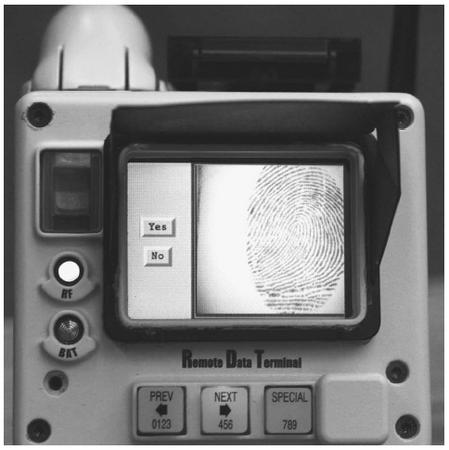
There are two major methods of the identification of fingerprints—comparison of lifted prints and live scanning. The first method is mainly used in forensics, while the second is used for authentication purposes (in security applications) and is also slowly becoming a method for identification at some police stations.
Analysis and classification of fingerprints. Ridges present on the fingers are classified based on the patterns they form. The most important features are ridge endings and bifurcations (separation of a ridge into two). These features are called minutiae and form the basis for further classification and identification. Based on the forms created by the minutiae (loops, whorls, etc.) fingerprints are further sub-classified into many more distinct patterns.
Modern fingerprint analysis uses computer algorithms to determine the similarity between a print and images stored in a database. Analysis is usually performed on multiple levels. First, the algorithms are compared to the prints on the coarse level to identify a type of a print, and then subsequently to identify more and more details until a match is found. The computer analysis of prints compares ridges, bifurcations and their relative location. Fingerprint analysis software and scanners identify a set number of similarity points, this number being determined by the software used, typically up to 90 points are compared. After identification of a set number of features, a template of the scanned print is formed and this is subsequently compared to the templates stored in the computer to determine if the print has a match. Although limiting the characteristics to be compared speeds up the matching process, it can also affect the accuracy if inadequate numbers are compared. Accuracy also depends on the application for which the fingerprint analysis is used.
Scanners have comparison algorithms and a number of recognizable characteristics programmed in, together with the prints of the users (enrolment) to provide the templates for comparison. The FBI fingerprint system is over 98% accurate, while the authentication systems accept only 97% of authorized users. Among some of the reasons for the rejection are: scars, calluses, cracks, dirt, or excess fingernail length.
Fingerprint analysis tools. Two types of fingerprint scanners are normally used, optical scanners and capacitance scanners. Optical scanners identify the print using light; depending on the brightness of the reflected light, optical scanners depict ridges as dark and valleys as light. Capacitance scanners determine the print by using an electrical current. Valleys and ridges on the fingers produce different voltage output, allowing for discrimination between them.
As sophisticated they are, the existing scanners are not totally immune to fraud. Optical scanners can be fooled by a picture, whereas the capacitance scanners can be fooled by a mold of a finger. Some scanners also have temperature and pulse sensors, but they are still vulnerable to molds placed over real fingers.
A number of portable fingerprint scanners were developed mainly by computer companies to provide a secure access for the users. In 1998, Compaq was the first to have a print reader attached to the computer. Currently, there are multiple systems for use with desktop and laptop computers in the form of PC cards and biometric mice. A portable print reader used for computer security employs a tiny digital camera to take a picture of a print and convert it into a map that is subsequently stored in the computer and cannot be duplicated.
Commercial fingerprint identification systems were introduced over 15 years ago. They are now used in security applications to gain access to a building or areas within the building, or computers or network access. Some companies, police offices, and high-security government buildings require fingerprint identification for access to the building or its selected parts.
In order to protect sensitive data, some businesses and the military often use scanners that are attached to computers (the U-Match mouse, for example) or installed in keyboards. These provide either immediate identification for access to the terminal or remote identification for access to secure documents or archives. NATO facilities in Turkey, and the U.S. Office of Legislative Council uses similar technology. New scanner trials are on the way to provide the same protection for e-commerce and Internet banking in order to secure transactions.
In order to combat cell phone thefts, the industry is considering equipping phones with fingerprint readers. Fingerprint protection is also offered for a new generation of safes, such as those provided by Biometrics Marketing. Finally, the scanners are being used to replace timecards in companies and to integrate payroll systems. Five U.S. airports, including Chicago's O'Hare have installed finger-print scanners to check employees' backgrounds. Some banks use fingerprint scans before a check is cashed. Similarly, government agencies sometimes utilize fingerprint scans to ensure that payments are given to the proper recipients.
Today, fingerprint analysis technology is the most wide-spread biometric method of identification and authentication for forensic and security purposes.
█ FURTHER READING:
BOOKS:
Ashbourn, Julian. Advanced Identity Verification: The Complete Guide. London: Springer Verlag, 2000.
Nanavati, Samir, Michael Thieme, and Raj Nanavati. Biometrics: Identity Verification in a Networked World. New York: Wiley and Sons, 2002.
ELECTRONIC:
Find Biometrics. < http://www.findbiometrics.com/index.html > (14 December 2002).
NCSC. "Individual biometrics." < http://ctl.ncsc.dni.us/biomet%20web/BMFingerprint.html > (14 December 2002).
Comment about this article, ask questions, or add new information about this topic: