Closed-Circuit Television (CCTV)
█ LARRY GILMAN
Closed-circuit television (CCTV) involves the use of video cameras to produce images for display on a limited number of screens connected directly to a non-broadcast transmission system (e.g., a network of cables). Commercial cable TV is, technically, an example of CCTV, but the term "closed-circuit TV" is generally reserved for systems serving a small number of screens that are monitored for security purposes. CCTV is a ubiquitous feature of institutional security systems. It is employed by prisons, banks, urban police forces, airports, military organizations, utilities, large corporations, various other organizations, and wealthy individuals. Some specific applications of CCTV are:
- X-ray baggage-inspection devices at airports.
- Remote viewing of dangerous industrial processes, rocket liftoffs, and other operations.
- Perimeter security around power plants, military installations, warehouses, police stations, and other defended facilities.
- Intrusion or theft monitoring of secure spaces, whether indoors (halls, lobbies, specific doors and rooms, etc.) or outdoors (parking lots, automatic teller machines, loading docks, etc.).
- Monitoring of vehicular traffic for traffic-control purposes or detection of illegal activity (speeding, smuggling, etc.).
- Identity-checking of persons desiring entry into a building.
- Computerized recognition of individual faces, with possible identification of "wanted" persons.
Two of the most important CCTV applications are discussed in more detail below.
Perimeter security. Prior to CCTV, in order to secure the perimeter of an area, it was necessary to post guards in such a way that their lines of sight covered the entire circumference of the area. With CCTV, it is possible to reduce the number of personnel needed to secure a perimeter by placing TV cameras at strategic points and transmitting the resulting images to a control room where a few guards can monitor many screens. Ideally, these observers will note any suspicious event on their screens and alert a response team. CCTV has thus for decades been a component of the typical Perimeter Intrusion Detection System (PIDS), which combines CCTV with devices designed to detect intrusion by other means (ultrasonic movement detectors, window alarm-contacts, etc.).
CCTV technology, however, has not proved as effective in PIDS applications as was once hoped. As vigilance studies by psychologists confirm, guards who spend hours "screen gazing" at static scenes (> 20 minutes, in tests) tend to become bored and less efficient, and are then likely to miss low-frequency events, such as a figure running up to and climbing over a fence. In the words of Geoff Thiel, a British CCTV-security expert, "Contrary to popular belief, impressive control rooms with large banks of monitors generally do not provide an effective "real time" surveillance service. The vast majority of installed CCTV cameras remain unwatched and incidents are not likely to be detected while they are occurring. CCTV is therefore reduced to a "post-mortem" tool…" (1999 International Carnahan Conference on Security Technology).
Starting in the 1980s, designers sought to combat the bored-guard effect by using automatic Video Motion Detectors (VMDs). These devices are designed to automatically detect scene action by comparing successive image-frames for changes. When change is detected that exceeds a predetermined threshold, an alarm is sounded. A guard then judges whether the alarm is false or valid.
VMDs, however, have not turned out to be a security panacea. There are too many sources of image change, especially in outdoor scenes, for a simple circuit to distinguish meaningful intrusions from nuisance alarms: shifting shadows, wind-shaken foliage, birds, rodents, blowing trash or leaves, camera movement, camera auto-iris adjustments, and the like. Faced with frequent false VMD alarms, guards tend to ignore the system altogether. VMD use is therefore restricted to artificially-lighted indoor spaces or to expensive systems that employ computer processing to reduce the false-alarm rate.
In the 1990s and beyond, artificial intelligence techniques—in particular, expert systems—have been combined with VMD to increase the effectiveness of CCTV. An expert system applies higher-level processing to information extracted from the pixels of the raw CCTV image in order to identify and track objects, usually including human intruders. Such systems are a definite improvement over simplistic VMD, and have proven their potential to ignore waving tree-limbs and rabbits hopping over lawns. However, progress remains slow, as in all artificial-intelligence efforts to navigate uncontrolled, complex, real-world situations. A large number of explicit classification rules, for example, must be generated to enable a program to "understand" a given scene—and a scene may change its appearance radically depending on weather (e.g., fog, snowfall, rain), time of day, number and type of cars in the parking lot, and numerous similar factors. It is,
therefore, difficult to make a PIDS expert system expert enough to be authentically useful. PIDS designers continue to emphasize that there is no near prospect of intelligent CCTV systems outperforming human guards, with all their weaknesses.
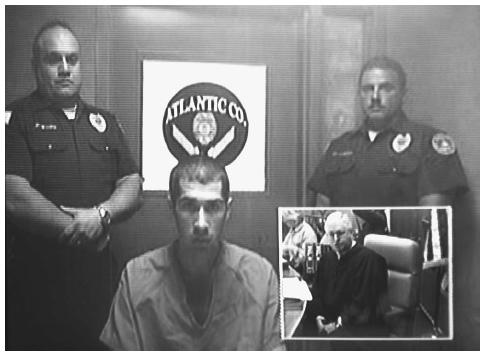
Public-surveillance CCTV. Surveillance by police of sidewalks, train stations, courtyards, parking lots, and other public spaces has proliferated rapidly throughout Europe and the United States during the last decade, propelled largely by the increased availability of inexpensive electronics. Many major cities, including Copenhagen, London, New York, and Washington, D.C., now possess public-surveillance CCTV systems, most often operated by police departments. In some cases, images from these systems are being processed using facial recognition systems (also termed biometric systems, from the Greek for "life measurement"). Facial recognition systems are software algorithms that seek to extract telltale facial features from video images and match faces in photographs to those in a database. Public-surveillance systems are thus advertised as serving two basic purposes, deterrence of crime in watched areas and identification of wanted persons.
Such systems have been criticized on several grounds. In Britain, where public-surveillance CCTV has been in use since the 1980s, studies have cast doubt on whether CCTV has any tendency to reduce crime through deterrence. Crime sometimes decreases in monitored areas, but many criminologists argue that this is because criminals simply move their activities elsewhere. Further, facial-recognition software has an extremely low success rate. Several systems, including ones deployed by the city of Tampa, Florida and by the U.S. Immigration and Naturalization Service, have been abandoned within months of deployment due to their zero or near-zero success rates. Police databases have also occasionally been used by individuals with access for illegal purposes (e.g., stalking exspouses, blackmailing), and public-surveillance CCTV systems, like any powerful surveillance tool, are vulnerable to such abuse. Further, system operators, who are usually male, sometimes use CCTV systems to voyeuristically observe women; a British study found that 1 in 10 women were targeted for voyeurism by the operators of one public-surveillance system. Studies of operators of public-surveillance systems have also shown instances of selectively monitoring dark-skinned persons. Further, powerful surveillance tools may offer a tempting aid to repression of groups such as political protestors. Many aspects of public-space behaviors that are quite legal are nevertheless confidential or at least personal by nature—courtship behaviors, travel patterns, buying habits, lawyer/client consultations, reading choices, smoking, and more. Many persons dislike the idea of such behaviors being recorded by government officials as a matter of course.
There is also widespread willingness in some countries, however, to give up a large measure of privacy in the quest for security from terrorism. A survey conducted by Business Week in November, 2001 found that 63% of U.S. adults favored increasing use of public-surveillance CCTV and that 86% favored the use of facial-recognition software to scan for terrorists in public places (as was done with taped images of over 100,000 attendees at the 2001 Superbowl). CCTV, enhanced by computer processing, will probably play a growing role in both its traditional security applications and in public life in years to come.
█ FURTHER READING:
BOOKS:
Nieto, Marcus, Kimberly Johnston-Dodds, and Charlene Simmons. Public and Private Applications of Video Surveillance and Biometric Technologies. Sacramento, CA: California Research Bureau, California Public Library, 2002.
PERIODICALS:
Notton, John. "The Use of Technology in Policing the City of London," in proceedings from the International Carnahan Conference on Security Technology, Larry D. Sanson, ed., IEEE, 35–39, 1998.
Sage, Kingsley, and Steward Young. "Computer Vision for Security Applications," in proceedings from the International Carnahan Conference on Security Technology, Larry D. Sanson, ed., IEEE, 210–215, 1998.
Thief, Geoff. "Automatic CCTV Surveillance: Towards the VIRTUAL GUARD," in proceedings from the International Carnahan Conference on Security Technology, Larry D. Sanson, ed., IEEE, 42–48, 1999.
Walters, Peter. "CCTV Operator Performance and System Design," in proceedings from the International Carnahan Conference on Security Technology, Larry D. Sanson, ed., IEEE, 32–37, 1993.
ELECTRONIC:
American Civil Liberties Union (ACLU). "What's Wrong With Public Video Surveillance?" < http://archive.aclu.org/issues/privacy/CCTV_Feature.html > (December 19,2002).
SEE ALSO
Biological and Biomimetic Systems
Bio-Optic Synthetic Systems (BOSS)
Biosensor Technologies
Comment about this article, ask questions, or add new information about this topic: